, 3 min read
Cisco 2014 Annual Security Report: Java continues to be most vulnerable of all web exploits
Cisco provides a report on computer security which contains a number of key findings:
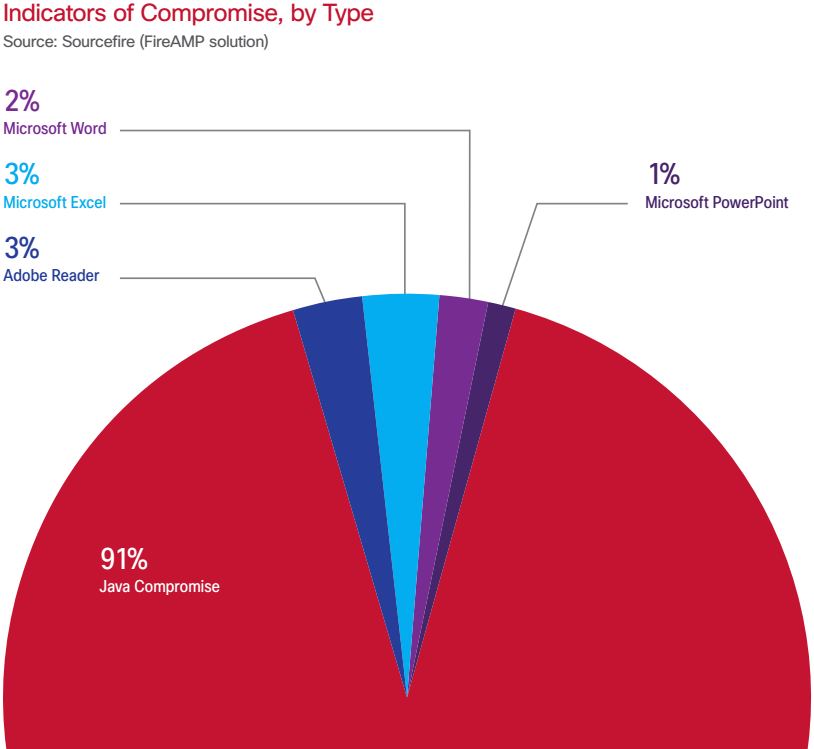
- Java comprises 91% of all web exploits.
- 99% of mobile malware targets Android.
- Java is the exploit that criminals choose first, since it delivers the best return on investment.
- In the aftermath of the Boston Marathon bombing two large-scale spam campaigns commenced. Both campaigns carried subject lines about news bulletins. The links directed recipients to malicious iframes designed to infect visitor's computers.
- Global spam volume is dropping.
- Many users download mobile apps regularly without any thought of security.
- 64% of all malware categories are trojans.
- Most malware come from online-games.
- A steady decline in unique malware hosts and IP addresses suggests that malware is being concentrated in fewer hosts and fewer IP addresses.
- Brute-force login attempts increased threefold.
- Many CMS compromises can be traced back to plugins written in PHP that were designed poorly and without security in mind.
- The rise in cloud computing is undeniable and unstoppable. Cisco has projected that cloud network traffic will grow more than threefold by 2017.
- The reality is that it's no longer a matter of if attackers get in, but when.
Cisco used the following data
- 16 billion web pages
- 93 billion e-mails
- 200.000 IP addresses
- 33 million endpoint files
I first read on this in eWeek.
Java security was in the press repeatedly in 2013, see for example
- Alert (TA13-064A) Oracle Java Contains Multiple Vulnerabilities, an attacker could execute arbitrary code on a vulnerable system with the privileges of the Java plug-in process
- Kritische Schwachstelle in aktueller Java-Laufzeitumgebung, BSI empfiehlt Internetnutzern Deaktivierung von Java (in German)
- Objet : Vulnérabilités dans Oracle Java, Ces vulnérabilités sont activement exploitées et largement diffusées (in French)
Added 18-Aug-2024: In Cisco Talos Year in Review 2023 the top targeted vulnerabilities are as in below table. Java is still in the top ten.
| Ranking | CVE | Vendor | Product | CISA finding |
|---|---|---|---|---|
| 1 | CVE-2017-0199 | Microsoft | Office and WordPad | Routinely exploited in 2022 100/9.3 |
| 2 | CVE-2017-11882 | Microsoft | Exchange server | Routinely exploited in 2022 100/9.3+ |
| 3 | CVE-2020-1472 | Microsoft | Netlogon | Routinely exploited in 2022 100/9.3 |
| 4 | CVE-2012-1461 | Gzip file parser utility | Multiple antivirus products | |
| 5 | CVE-2012-0158 | Microsoft | Office | Commonly exploited by state-sponsored actors from China, Iran, North Korea, and Russia (2016-2019) |
| 6 | CVE-2010-1807 | Apple | Safari | |
| 7 | CVE-2021-1675 | Microsoft | Windows (print spooler) | |
| 8 | CVE-2015-1701 | Microsoft | Windows (kernel-mode driver) | |
| 9 | CVE-2012-0507 | Oracle | Java SE | |
| 10 | CVE-2015-2426 | Microsoft | Windows font driver |